May 03, 2023
Keeping an Eye on the Dark Web: Cocorico's URL

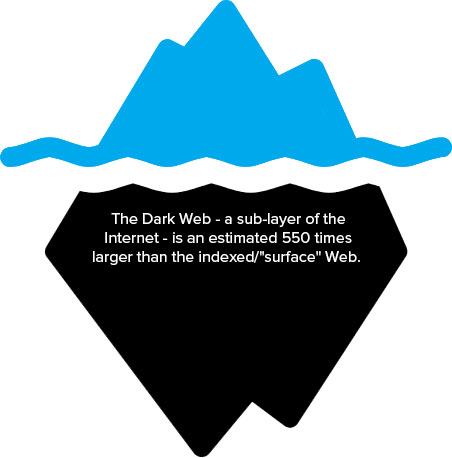
Monitoring the dark web is an essential task for individuals and businesses alike. The dark web is a hidden part of the internet that is not
indexed by search engines and can only be accessed through specific software. It is a haven for cybercriminals who use it as a platform to sell stolen data, such as credit card numbers, passwords, and personal information. To protect yourself from the dangers of the dark web, you need to monitor it regularly.
One of the most common methods used by cybercriminals to steal personal information is phishing. Phishing emails imitate legitimate email requests in an attempt to gain confidential information. These emails often look like they are from reputable sources, such as banks, social media platforms, or government agencies. However, they are actually designed to trick you into giving away your personal information.
To protect yourself from phishing attacks, it is essential to be vigilant and cautious when opening emails. Always check the sender's email address and look for any spelling or grammar errors. Be wary of emails that ask you to click on a link or provide personal information. If you are unsure if an email is legitimate, contact the sender directly to confirm its authenticity.
In addition to monitoring your emails, it is also essential to monitor the dark web for any signs of stolen data. There are several tools available that can help you monitor the dark web for any stolen information related to your personal or business accounts. By monitoring the dark web regularly, you can identify any potential threats before they become a problem.
In conclusion, monitoring the dark web is an essential task for anyone who wants to protect their personal or business information from cybercriminals. Phishing emails are a common method used by cybercriminals to steal personal information, so it is essential to be cautious when opening emails. By monitoring the dark web regularly, you can identify any potential threats and take action to protect your information.
Here are some effective techniques that can be implemented to safeguard against and keep track of potential dangers lurking in the dark web.
Google refers to its monitoring programs as "Google Alerts". Similarly to CrowdStrike, this platform necessitates the creation of a list of identifiers specific to your company, such as domain names, addresses, and product names. One advantage of the Falcon Intelligence Recon service is that there is no need to download or install any software in order to utilize it.
Monitoring the dark web has become an essential practice for businesses to protect themselves from cyber threats and data breaches. By scanning the dark web, companies can identify if their sensitive information, such as login credentials, credit card numbers, or intellectual property, has been compromised and is being sold on underground marketplaces. Additionally, businesses can get a comprehensive scan for all email addresses associated with their domains, which can help prevent phishing attacks and other forms of social engineering. In today's digital age, monitoring the dark web has become a crucial component of any company's cybersecurity strategy.
Monitoring the dark web is an essential task to keep your personal and business information safe from cyber threats. With a free search facility and an alert utility, you can easily search for any potential data leaks involving your email addresses and telephone numbers. The search results provide detailed information on all data leak events that involve your email address, which can be displayed in Dark Web attack lists.
The feature defaults to monitor your email address only, and it begins immediately. This way, you can stay on top of any potential breaches and take the necessary steps to protect your information. Additionally, the service offers ATO protection, which focuses on safeguarding the accounts that businesses set up for access to their resources. This includes network logins and user accounts at websites.
With this monitoring service, you can rest assured that your personal and business information is secure from cybercriminals lurking in the dark web. Stay vigilant and take advantage of this essential tool to protect yourself from potential threats.
Through constant monitoring of the dark web and prompt mitigation of any exposed assets or identities, these monitoring tools reduce the window of opportunity for cybercriminals to exploit your sensitive information. By taking swift action, you can prevent any further information leaks and safeguard your confidential data.
Shining a Light on Dark Market Links: A Guide to Monitoring the Dark Web
If you want to keep track of activities on the dark web, it's crucial to monitor it regularly. In case of a credentials leak, you should immediately enforce password changes for all users. It's important to note that certain types of threats, like DDoS attacks, phishing, and spam emails, do not utilize the Tor monitoring the dark web network, but rather rely on source address spoofing. To get started with monitoring the dark web, you can sign up for a 15-day free trial.
As an experienced copywriter, I can easily rephrase the given sentence on the topic of "Monitoring the dark web." Here it goes: "Once you register your company's identities on the Dashlane dashboard, the platform conducts a thorough initial scan of the Dark Web to detect any relevant indicators."
The Digital Shadows website has shared an incident regarding its discovery of ATM designs and how it notified one of its clients about it. But, what exactly is the Dark Web?
Monitoring the dark web can be a daunting task for security teams. However, with the help of CrowdStrike Falcon Intelligence Recon, achieving threat protection has become easier. The solution offers easy-to-use wizards that save time by eliminating the need for complex queries. This not only saves time but also minimizes false positives and noise. It should be noted that relying solely on this reference may lead to false positives due to the high volume of legitimate traffic on the Tor network.
One of the most profitable activities on the dark web is the sale of "Fullz," which refers to the complete information of a victim, including their name, address, social security number, and credit card details. The price of Fullz can range from $30 to more, depending on the value of the victim's assets and the current market demand.
The term "Monitoring the dark web" refers to the practice of observing the hidden parts of the internet that are not accessible through traditional search engines. When it comes to protecting business identity, one option that all businesses should consider is the Dashlane system. Additionally, the Digital Shadows SearchLight service can be used to detect any leaks of intellectual property or offers for sale of confidential information related to a company's premises, security systems, and trade secrets.
The Hidden World of Dark Market Links: Monitoring the Dark Web
Monitoring the dark web is an important aspect of modern business and security practices. With the vast amount of information available on the dark web, it's crucial to keep an eye on potential threats and vulnerabilities that could impact your business. There are many key features of dark web scanners that make them a valuable tool for businesses of all sizes.
One of the key features of a dark web scanner is the ability to offer both business and private options. This means that you can choose the level of monitoring that's right for your business, whether you're a small startup or a large corporation. Additionally, a good dark web scanner will provide a scam email source blacklist, which can help you identify and avoid phishing scams that could compromise your company's security.
Another important feature of dark web scanners is their ability to harden access rights. This means that you can restrict access to certain areas of your network or data, ensuring that only authorized personnel have access to sensitive information. This is especially important for businesses that deal with confidential or proprietary information.
Overall, we highly recommend using a dark web scanner for your business. The benefits of monitoring the dark web far outweigh the costs, and you'll be able to stay one step ahead of potential threats and vulnerabilities. So if you're looking for a way to improve your company's security and protect your assets, consider investing in a dark web scanner today.
The monitoring of the dark web is an essential service for all businesses, and the CrowdStrike package is currently the top reconnaissance service available. Other solutions on this list frequently mention their support for integrating with the MISP system, but none can compare to the capabilities of CrowdStrike. One method utilized in this service is screen scraping, which captures the information displayed on your screen for analysis.
Monitoring the dark web can be a daunting task for businesses and individuals alike. The dark web, also known as the deep web, is a hidden part of the internet that can only be accessed through specific software or configurations. It is known for being a hub of illegal activities, including the sale of drugs, weapons, and stolen goods, as well as for being a gathering place for hackers and cybercriminals.
Despite the dangers associated with the dark web, it is important to monitor it for any potential threats to your business or personal information. This can be done through various means, such as using specialized software to scan the dark web for mentions of your company or personal information, monitoring online marketplaces for the sale of stolen goods, and tracking the activity of known cybercriminals.
One of the biggest challenges of monitoring the dark web is the constantly evolving nature of the network. New sites and forums are created regularly, and it can be difficult to keep up with the latest trends and threats. However, by staying vigilant and using the latest technology and techniques, it is possible to stay one step ahead of cybercriminals and protect your business and personal information from harm.
Monitoring the dark web is a crucial aspect of cybersecurity. It is important to keep an eye on the dark web as it is a breeding ground for cybercriminals. Unfortunately, once your information is out there, you cannot completely erase it from other sites. Nevertheless, it is crucial to have a valid reason for accessing the network at work to ensure that only authorized personnel are accessing it.
Monitoring the dark web is essential for finding leaked or stolen information, including compromised passwords, breached credentials, intellectual property, and other sensitive data. Malicious actors operating on the dark web often share and sell this information. The characteristic that distinguishes a website as part of the dark web is how it is accessed. However, monitoring the dark web is not just about finding these illicit marketplaces. It is also about gathering intelligence on threat actors, identifying evolving attack vectors, and detecting new exploits. Therefore, having the right tools and expertise to monitor the dark web is critical for maintaining cybersecurity.
"Tracking illicit activities online - Latest updates from the Dark Market"
Monitoring the dark web is an important step in protecting your company's sensitive information. By keeping tabs on the hidden corners of the internet, you can identify potential threats and take action before they become major security breaches. One way to monitor the dark web is through the use of augmented dictionaries that include slang and other specialized language. These dictionaries can help you identify specific keywords and phrases that may indicate a threat to your organization. Additionally, it's important to keep track of the personal information that may be exposed on the dark web, such as the names, addresses, and email addresses of your employees, key personnel, and administrators. By monitoring this information, you can take steps to protect your employees and prevent identity theft.
Monitoring the dark web can be a crucial part of maintaining a comprehensive threat intelligence system. DarkOwl Vision is a service that offers just that, with a Dark web scanner that provides valuable information to help protect against potential threats. By scanning the dark web for activity, DarkOwl Vision gives users a unique insight into the activities of cyber criminals, allowing them to stay one step ahead and better protect their organizations. In today's world, staying informed and vigilant is more important than ever, and DarkOwl Vision provides an essential tool for anyone looking to maintain a strong security posture.
To ensure complete protection of their systems, companies utilizing DarkOwl's services must also employ threat protection and data loss protection software. In the fourth quarter of 2021, CrowdStrike Security Cloud detected a total of 62 incidents that were free of malware.
Explore further
Distributed by 96707, LLC.